item

René-Sylvain Bédard
What if... #Microsoft gave you everything you needed to create a #SECURE architecture?
//
Wednesday February 26, 2025 - 09:00
item

Vanessa Deschênes
Did you say AI? What about HI? An ex-CPO's story
//
Wednesday February 26, 2025 - 14:15
item

Dominique Derrier
Stories Of Mistakes
//
Wednesday February 26, 2025 - 14:45
item

Pierre LeCalvez
Stories Of Mistakes
//
Wednesday February 26, 2025 - 14:45
item

Guillaume Ross
FUDBusters!
//
Wednesday February 26, 2025 - 15:30
item
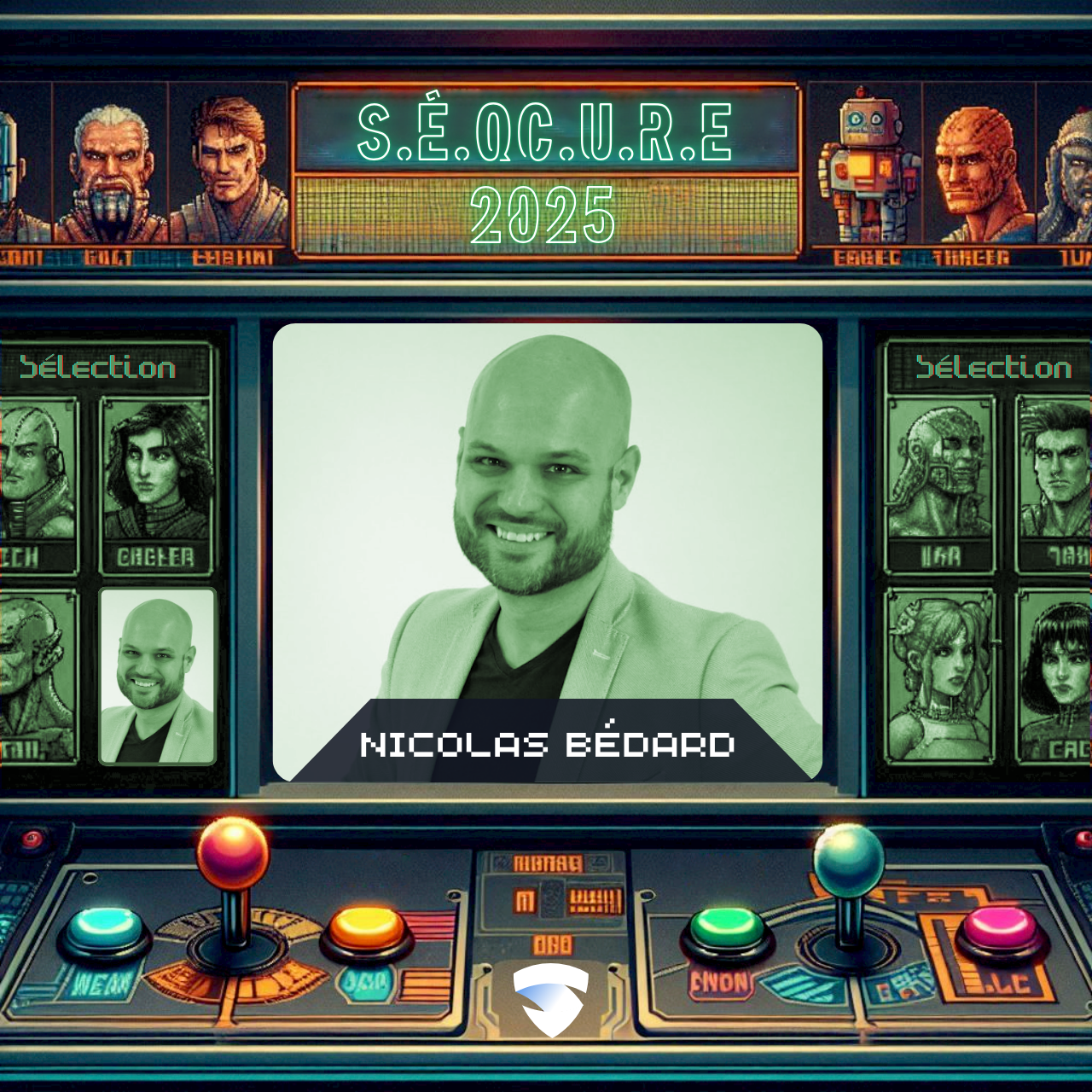
Nicolas Bédard
From Training to Inference, Protecting LLM Models against Cyberthreats
//
Thursday February 27, 2025 - 09:00
item

Steve Lavoie
Incident response in SMEs
//
Thursday February 27, 2025 - 10:30
item
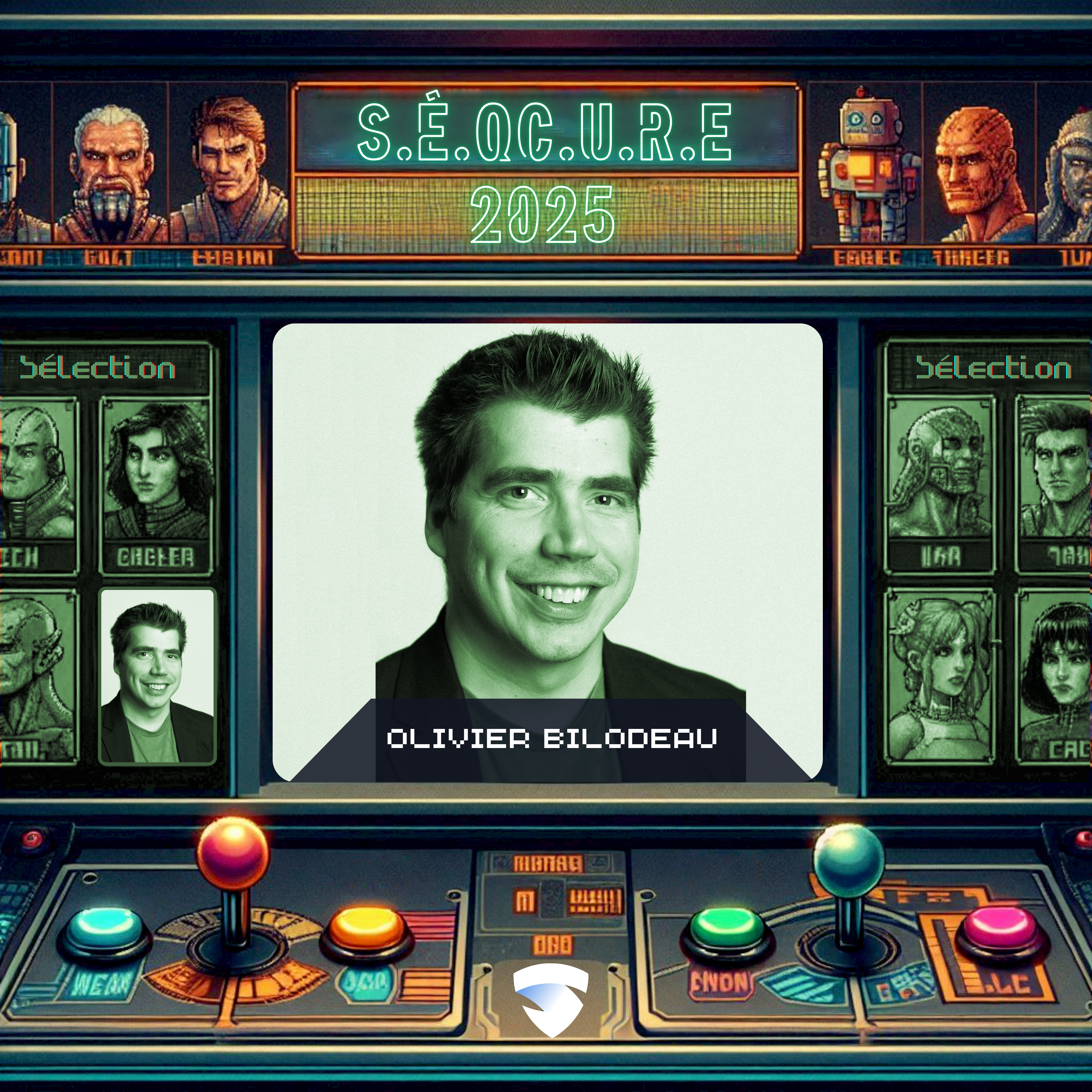
Olivier Bilodeau
Beyond infostealer malware: infection vectors, unusual stolen assets and countermeasures
//
Thursday February 27, 2025 - 13:15
item
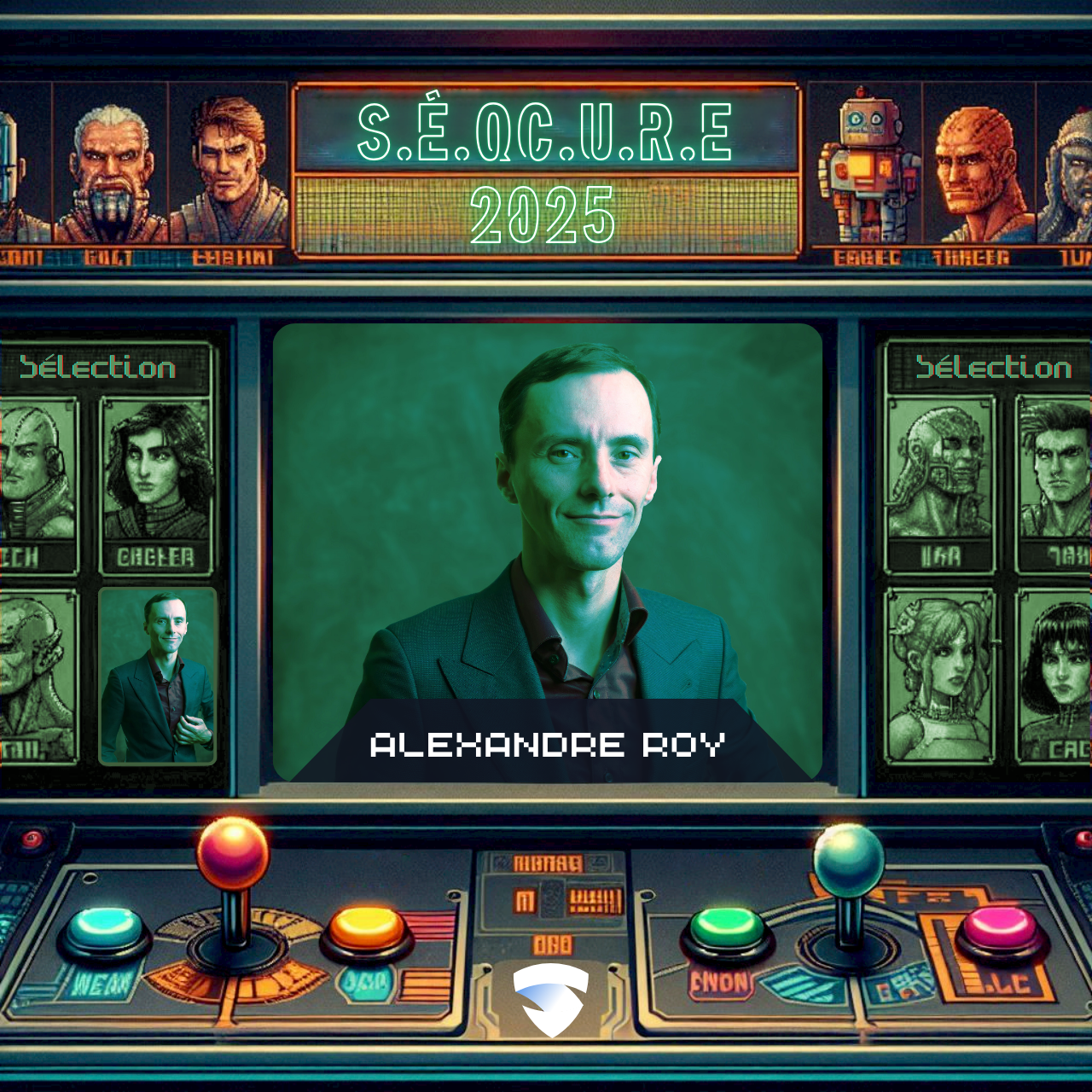
Alexandre Roy
Inspire, influence, secure: Strengthening information security through communication
//
Thursday February 27, 2025 - 14:45
item
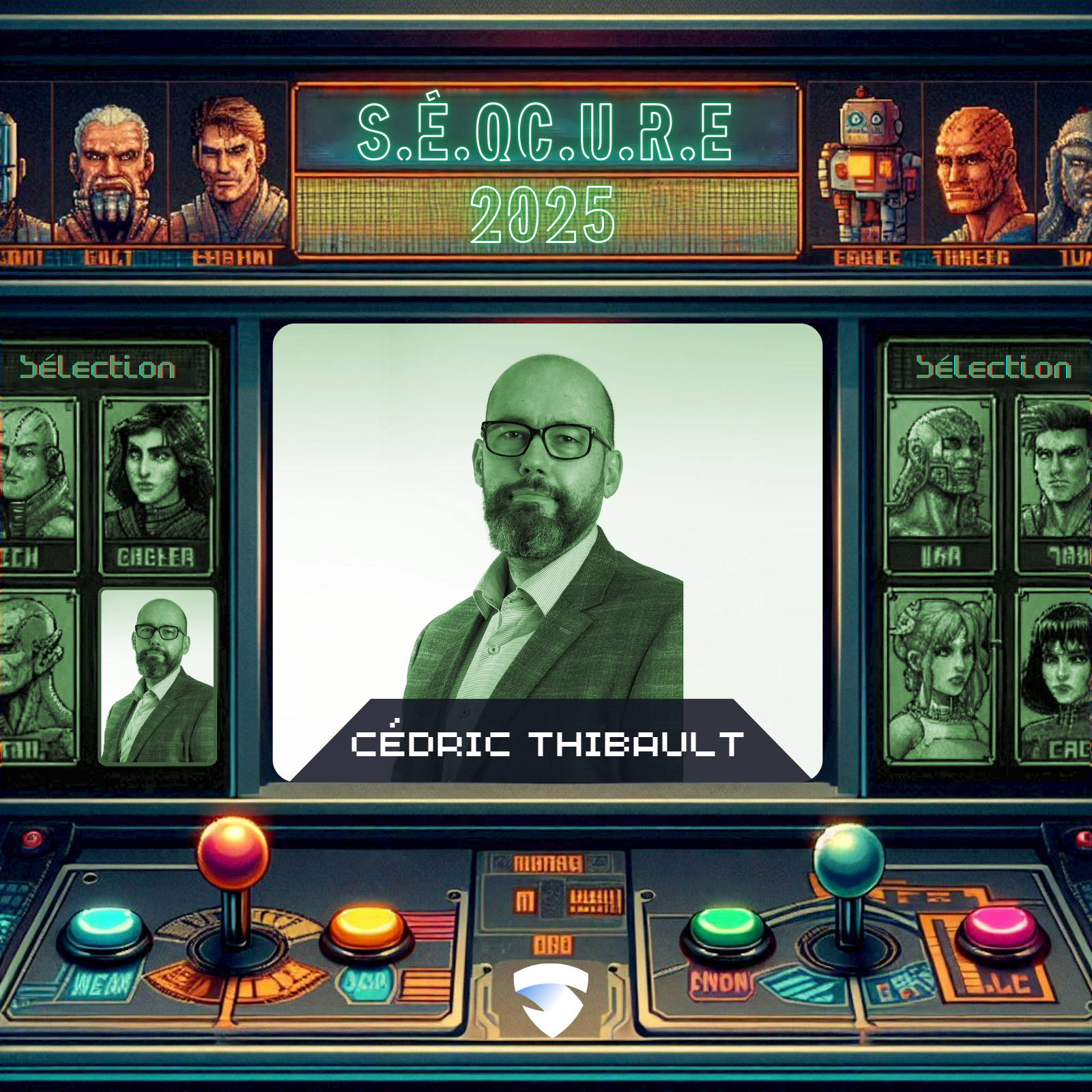
Cédric Thibault
Analysis and lessons learned from attacks on the Cloud
//
Thursday February 27, 2025 - 15:30